In 2019, the Pakistan Electronic Media Regulatory Authority notified television channels that they were not allowed to host the Pakistani Senator Hafiz Hamdullah on air. The reason: Hamdullah had been declared a “confirmed alien,” and his identity card had been “digitally impounded” by Pakistan’s National Database and Registration Authority (NADRA). NADRA began operations in 2000 by launching a biometric (fingerprints, facial, and iris recognition) computerized national identity card (CNIC). At NADRA, custom-made software integrates and verifies data from individuals as well as kin units, determining who is and is not a Pakistani citizen.
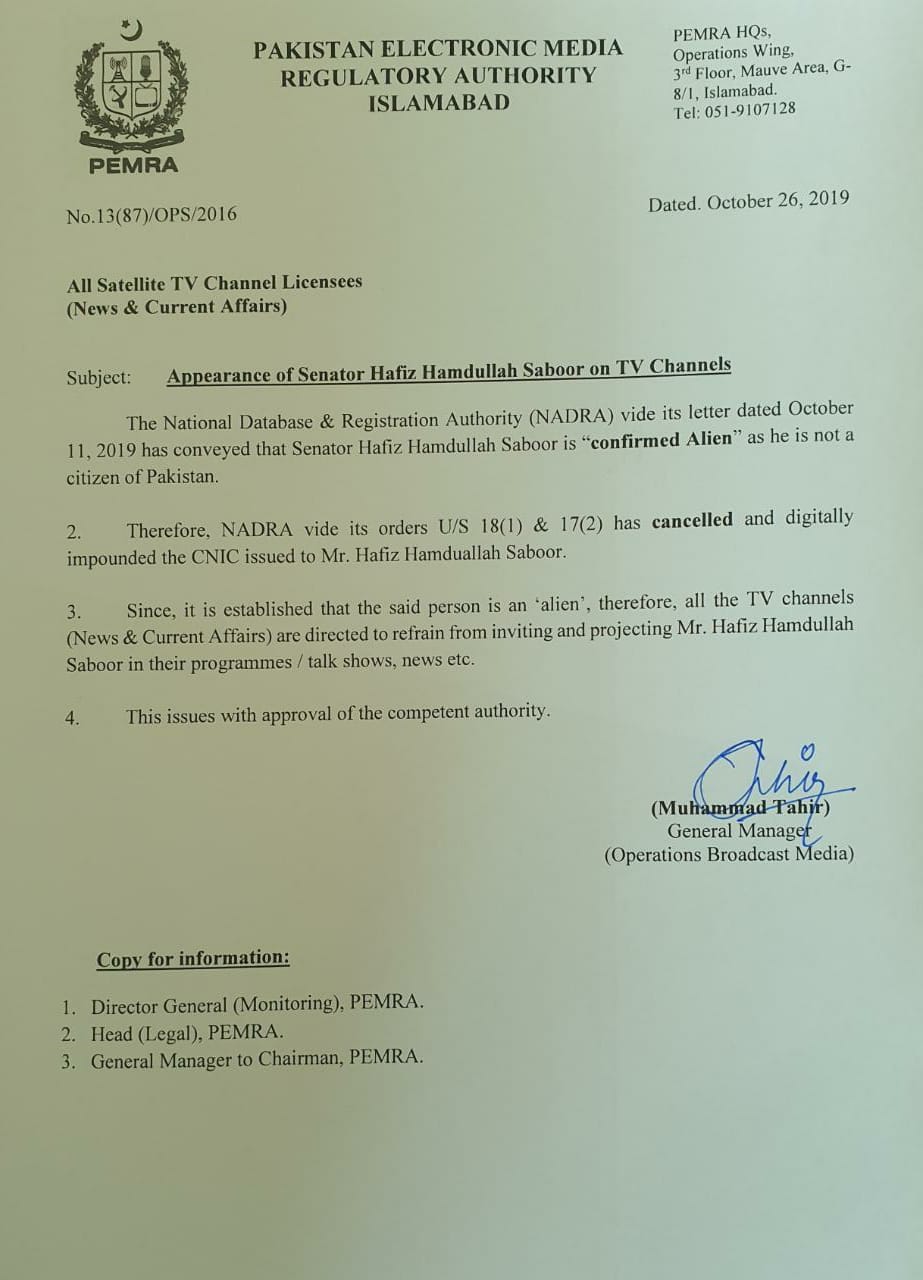
2019 notification to television channels from the Pakistan Electronic Media Regulatory Authority (Credit: Nadia S. Malik on Twitter) [1]
But how, exactly, did NADRA manage to declare a Pakistani legislator a “confirmed alien”? NADRA responded that Hamdullah’s identity card had first been blocked in 2018. According to NADRA’s protocols, a “block” on an identity card initiates a process of re-verifying citizenship[2]. Ultimately, NADRA declared Hamdullah a foreign national, and specifically Afghan, because he was unable to establish descent-based familial connections that would indisputably tie him to Pakistan. Importantly, it was his ancestors that were the problem for NADRA. Apparently, Hamdullah’s tribal affiliation to the Noorzai tribe, which had “origins in Afghanistan,” cast doubt on his national status[3]. Since Pakistan’s identification regime heavily relies on kin relations to determine citizen identity, kin connections become a dangerous, even contagious, source of “blockage” in the identity database. Those, like Hamdullah, who are “blocked” by NADRA must re-authenticate themselves as Pakistani nationals.
Perhaps counter-intuitively, such abrupt national exclusion by blocking does not equate to expulsion from the national identity database. Frequently, the record of the “blocked” person remains within the database, precisely so they cannot register in the identity database again at a later stage. Additionally, while the blocked cardholder may continue to physically possess the identity card, NADRA’s capacity for “digital impounding”—blocking the identity card in the database but not physically confiscating it—limits how the card can be used. Having a blocked card can curtail a range of activities, from buying a cell phone chip to property transactions. In fact, as NADRA’s identity card has become ubiquitous in daily life, it is only when people try to use the card that they find out that it has been blocked.
Like how infrastructural interruption reveals socio-political dynamics, I center the role of “blockage” for the study of an identity database. The quality of invisibility has long been understood as central to studies of infrastructure (Star 1999). Breakdown or interruption makes infrastructure visible. Tracking blockages in database systems as they ripple outwards into social and political life offers one way of doing an ethnography of databases.
The database extends into domains that may not, at first glance, appear “databased,” so to speak[4]. For an ethnography of a database, we must think with and beyond the technical and institutional infrastructures that produce database systems in their complexity and multiplicity.
Blocking, Sifting, and Flowing
The blocking of national identity cards in Pakistan functions as a kind of sifting, where verification processes operate as a sieve to differentiate between desirable and undesirable entities (Kockelman 2017). From here, we can follow how the design of the database builds into it the qualities that it seeks to sift. NADRA is not solely concerned with cyber-security and an “enemy” (Shannon 1946, quoted in Kockelman 2010) intercepting its highly securitized system. The day-to-day functioning of NADRA also reflects a preoccupation with “matter out of place” in the anthropological sense (Douglas 1996). Misfits in the database manifest as isolated identities who lack relatedness with others in the database, or perhaps even more unfortunately, like Hamdullah, happen to have the “wrong” kinds of relations.
NADRA, as an information infrastructure, communicates the identity of persons in Pakistan—as they go about their business, banking, voting, enrolling their children in school, or even getting on a bus. Thus, an obstruction in this channel—when an ID card does not work for someone—is just as important as when it does[5]. The structure of the database as the structure of kin relations enables both blockages and flows to do their work: even when NADRA “messes up” and blocks the wrong person[6], that blockage reveals that a verifiable citizen within this schema must be one who is connected to someone else.
At first sight, a database can appear as a singular container of information. In fact, the relational nature of a database, which makes many databases one, and one many, is a function of its form. Distinct pieces of information are only brought together through a simple and yet supremely useful technology: the query. The query, as language, is more than a metaphor[7]. The query brings distinct entities together to access information from a database. In so doing, entities are connected through a relation. It is this relational capacity that is one of the most significant features of large, networked databases. To query is to locate an entity. But importantly, that location is always done through its relation.
The conceptual significance of relationality, and relations in general, extends to a set of methodological questions: what would it look like to follow relations, both databased and social? An ethnography of databases would ask the question how? How is the individual disaggregated into its relations, both datafied and lived, in order to become authenticated and verifiable again?
Relational Responses to Relational Databases
Identification in this mode, through relatedness, produces social effects for those it brings into its datafied network. This occurs in two ways. First, if a family member’s identity card is blocked—if one individual within a family unit is suspected of being a foreign national—that blockage can spread almost contagiously to the rest of their family. Second, in response, family members with functioning identity cards can be recruited to vouch for those who are blocked. Following blockages out of NADRA’s offices and into the realm of social life, where they proliferate upon contact, reveal how they are not one-time occurrences, accidents, or aberrations. The capacity of flows and blockage are crucial instruments that transform informational systems into systems of control. Let’s turn to an example to explain this further.
Hamida Bibi is a woman who lives in Alipur Farash, a neighborhood in Islamabad where residents of an informal settlement (katchi abadi) were resettled more than twenty years ago. In 2015, she received a notice from NADRA stating that she was under “citizenship re-verification.” In describing the events that had provoked this, she said “my eldest son had a motorcycle repair shop, which he ran with a Kabuli (Afghan refugee) called Nabeel. They were renewing the lease on their shop, and in that context, Nabeel asked my son for his identity card as well as our (the parents) cards too. We gave them. What did we know? Later, Nabeel and his family took the (repatriation) packages they were giving at the time to Afghan refugees (muhajirs) to go back to Afghanistan. It was just after a few months after this that I received this notice from NADRA”[8]. Hamida Bibi was sure that Nabeel had used Hamida and her husband’s identity cards—claiming they were his parents—to get his own identity card.
Over subsequent conversations, I learned that there was a relation (rishtidari), albeit circuitous, between Nabeel and Hamida Bibi’s family. Bear with me: Nabeel was Hamida’s daughter-in-law’s sister’s husband’s sister’s husband. It was for this reason, Hamida explained, that they trusted him with their identity cards. “Now we have learned our lesson, and we would never give any document even to our closest relative.” This sentiment of withholding, or blocking access to documents in the context of blocked identities, was one that was echoed during my fieldwork by many others in a similar situation. Hamida’s daughter-in-law, Gulmina, present at this time, explained “this situation has caused such problems in my own family. I can’t go to my sister’s house anymore because Nabeel’s side of the family might be there!” In addition, Gulmina’s daughter had a heart condition and so had to regularly go for appointments to the Military Hospital in Rawalpindi. “It is an army hospital, so they always ask for an identity card. Every time we go, I have to ask my brother—whose identity card isn’t blocked—to go with us. If an emergency happens, I have to be dependent on my brothers? Is this why they married me into this family?!” Not only did blocked identities proliferate across extended relations, but they also produced a complex series of resentments, dependences, and pressures amongst relations: Hamida’s distrust of sharing her documents with her relations, Gulmina’s restricted access to her own sister’s home, as well as an increased inter-dependency with some kin (Gulmina’s brothers) over others.
The role of relations in producing blockage is mirrored in attempts at generating flow again, that is, in order to “unblock” identities. In her discussion of phatic labor, Julia Elyachar (2010) describes how everyday communicative channels serve an infrastructural function for political economy—just as train tracks, bridges, or telephone lines might. An ethnographer of databases can follow this insight to track how social practices, along with technological protocols, produce infrastructural outcomes in their own right. This can be seen in Hamida Bibi’s approach towards getting her identity card unblocked. In addition to deploying her sons for various trips to the NADRA offices, as well as using her sister-in-law as mediator to convince her husband that this was necessary (since he told Hamida to give up on it), she also got her brothers and a neighbor who worked at NADRA involved. “My brothers’ cards were never blocked. I am so fortunate, they have said to me multiple times, let us know what you need and we will even go with you. Only one of my brothers, who is paranoid and weak (kamzor) said he was too afraid that my blocked card would get his card blocked too”[9]. In contrast, Hamida had many grievances (gilay) about her neighbor, Shazia, who worked at NADRA. When Hamida went to the NADRA office and saw Shazia there, she complained, “Shazia’s eyes were ‘up here’ on her forehead. She wouldn’t meet my gaze and pretended as if we hadn’t known each other for years!” Hamida told me that going through the unblocking process, she recognized who was truly supportive and loyal and who would abandon you the second you need anything from them.
While joyous celebrations are not commonly associated with bureaucratic interactions, Hamida Bibi threw a party when her card was finally unblocked in 2019 (after close to five years). When she called me she said, “I am inviting everyone who has helped and supported me through this whole process.” This was pointed at the fact that there were some people who had not been very helpful, and that “they would not be getting any biryani.”
While NADRA deploys kin relatedness as the basis of identification, it reflects the capacity of databases in general to relate entities. This particular identity database is good to think about the many relational databases increasingly part of our everyday lives. In particular, by foregrounding blockage—generated from an intersection and interaction between social and technological practices—the database ethnographer must attend to the strategies, negotiations, and relational channels of communication, exemplified here by Hamida as well as Gulmina, in their attempts to deal with the movement of identifying information.
In designing an ethnography of a database, I had to think beyond database design and structure—in part because some aspects of technological design would always remain inaccessible to me, as they do for many researchers (Seaver 2017). Hamida Bibi and many others in her situation expanded the parameters of my ethnography as I was compelled to consider how experiences and connections between kin, or social relations more generally, become central to blockages and flows in an identity database.
References
Douglas, Mary. 1966. Purity and danger: an analysis of concepts of pollution and taboo. London: Routledge and Kegan Paul.
Elyachar, Julia. 2010. “Phatic Labor, Infrastructure, and the Question of Empowerment in Cairo.” American Ethnologist 37(3):452-4
Kockelman, Paul. 2010. “Enemies, Parasites, and Noise:How to Take Up Residence in a System Without Becoming a Term in It.” Journal of Linguistic Anthropology 20, no. 2 (2010): 406–21.
Poster, Mark. 1995. “Databases as Discourse, or Electronic Interpellations.” In The Second Media Age (pp. 78-94). Cambridge: Polity Press.
Seaver, Nick. 2017. “Algorithms as Culture: Some Tactics for the Ethnography of Algorithmic Systems.” Big Data & Society, (December 2017).
Serres. 2007 [1980]. The Parasite. Minneapolis: University of Minnesota Press.
Shannon, Claude E. 1946. “Communication Theory of Secrecy Systems,” first appeared in “A Mathematical Theory of Cryptography,” Sept.1, 1946.
Star, Susan Leigh. 1999. “The Ethnography of Infrastructure.” American Behavioral Scientist 43(3)
Footnotes
[1] On the top left-hand corner of the notification is the PEMRA logo consisting of a shield surrounded by a wreath, lying below a star nestled within a crescent moon. On the top right-hand corner is the PEMRA headquarters address, noted as Operations Wing, 3rd Floor, Mauve Area, G-8/1 Islamabad, Tel: 051-9107128. The notification number is 13(87)/OPS/2016. The text of the notification is as follows.
Subject: Appearance of Senator Hafiz Hamdullah Saboor on TV Channels
The National Database and Registration Authority (NADRA) vide its letter dated October 11, 2019 has conveyed that Senator Hafiz Hamdullah Saboor is “confirmed Alien” (quoted text appears in bold) as he is not a citizen of Pakistan.
Therefore, NADRA vide its orders U/S 18 (1) and 17 (2) has cancelled (word appears in bold) and digitally impounded the CNIC issued to Mr. Hafiz Hamdullah Saboor.
Since, it is established that the said person is an ‘alien,’ therefore all the TV channels (News and Current Affairs) are directed to refrain from inviting and projecting Mr. Hafiz Hamdullah Saboor in their programmes / talk shows, news etc.
This issues with approval of the competent authority.
After the text in the body of the notification, on the bottom right hand corner is a signature in blue ink by Muhammad Tahir, General Manager, Operations Broadcast Media. Below it, on the bottom left hand corner, is a note with the following text: Copy for information (text appears in bold): Director General (Monitoring), PEMRA, Head (Legal) PEMRA, and General Manager to Chairman, PEMRA.
[2] There have been numerous news reports of blocked identity cards, and their implications for those affected, such as this discussion in The Nation.
[3] In Hamdullah’s case, the Islamabad High Court did not concur with NADRA’s decision and asked for a reversal. In this way, different institutions of the state did not all act in concert, and the friction of the case generated its own politics.
[4] Mark Poster foregrounds how networked databases can share information and track an individual across distinct collections of information. “What is most important about discourses for Foucault is that they constitute their objects” (Poster 1990: 88). A uniquely identified individual is thus conjured, as an object, through the technology of the identity database. Poster brings into relief the stakes and affordances of large-scale, networked databases today, where the “individual” within the relational database is produced in domains even if they have not recognized it yet.
[5] As quoted in Kockelman (2010): “systems work because they do not work. Nonfunctioning remains essential for functioning” (Serres 2007[1980]: 79).
[6] As has happened to thousands of Pakistani tribal Pashtuns, frequently because of their connections to those who have already been designated as Afghan within NADRA’s database.
[7] Concretely, I am thinking of Standard Query Language (SQL), used to communicate with relational database management systems.
[8] It is possible, and a few NADRA officials mentioned this to me, that NADRA worked with UNHCR and the Afghan government to make a database of refugees who had taken the repatriation packages – which would confirm that they were refugees. Thinking through the network capacities, to cross-check identities in two databases, they were able to identify those who were in both.
[9] Ultimately, it was Hamida’s brothers’ documents and guarantee that allowed her identity to be unblocked.

1 Trackback